Introduction
Imagine your WordPress website, a platform you’ve carefully built and nurtured, suddenly displaying spammy pharmaceutical ads, redirecting visitors to dubious drug stores, or showing search results filled with illicit drug keywords. This is the notorious “WordPress Pharma Hack,” a pervasive and damaging form of SEO spam that targets WordPress sites. This hack not only tarnishes your site’s reputation and user experience but can also lead to severe SEO penalties, including de-indexing from Google, and a significant loss of organic traffic.
The Pharma Hack is particularly insidious because it often operates stealthily, injecting hidden content and links that are visible to search engine crawlers but not always to regular site visitors or even the site owner. This comprehensive guide will equip you with the knowledge and steps needed to understand, detect, remove, and prevent the WordPress Pharma Hack, ensuring your website remains clean, secure, and trustworthy in 2025.
What is the WordPress Pharma Hack?
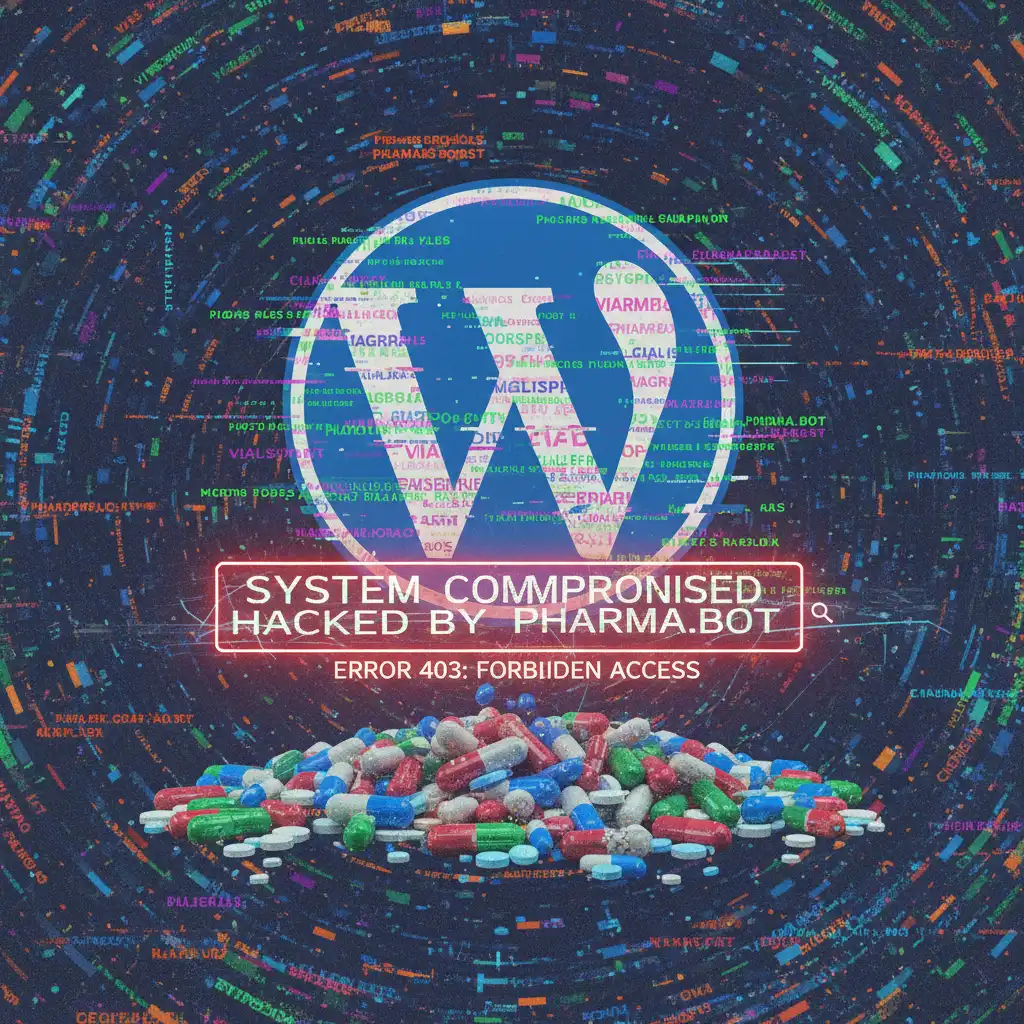
The WordPress Pharma Hack is a type of SEO spam where attackers inject hidden content, links, and new pages related to pharmaceuticals (e.g., Viagra, Cialis, weight loss drugs) onto a compromised WordPress website. The primary goal is to manipulate search engine rankings for these illicit products, leveraging your site’s authority to boost their own spammy or malicious sites. These injected pages are often cloaked, meaning they show different content to search engine bots than to human visitors, making detection difficult.
Key characteristics of this hack include:
- Hidden Content: Spam content is often hidden using CSS (
display: none;,visibility: hidden;), JavaScript, or by placing it off-screen, making it invisible to casual browsing. - New Spammy Pages/Posts: Thousands of new pages or posts with pharmaceutical keywords and often random URLs might be created on your site.
- Search Result Manipulation: Your legitimate search results in Google might show spammy titles and descriptions related to pharmaceuticals.
- Redirects: Visitors might be redirected to other malicious pharmaceutical websites when they click on your site’s links in search results.
- Unauthorized User Accounts: Sometimes, new administrator accounts are created to maintain access.
- Modified Core Files: Malicious code is often injected into core WordPress files, themes, or plugins.
How to Detect the WordPress Pharma Hack
Early detection is key to minimizing damage. Here’s how to identify if your site has been compromised:
1. Check Google Search Results for Your Site
This is often the first and most obvious sign. Perform a Google search for your website using the site: operator (e.g., site:yourdomain.com). Look for:
- Unfamiliar Pharmaceutical Titles/Descriptions: If your search results show titles or snippets related to Viagra, Cialis, or other drugs, your site is likely infected.
- Spammy URLs: Look for URLs with random characters or pharmaceutical terms that don’t belong to your site.
2. Google Search Console Warnings
If your site is verified in Google Search Console, Google will often notify you directly about security issues.
- Security Issues Report: Check the “Security & Manual Actions” section for warnings about “Hacked site” or “Spammy content.”
- Performance Report: A sudden drop in impressions or clicks, or an increase in “Crawled – currently not indexed” pages, can also be an indicator.
3. Inspect Your Website Files
Attackers often inject malicious code into core WordPress files, themes, and plugins. Access your files via FTP or your hosting file manager.
index.php(root, theme, plugin folders): Look for suspicious code, especially at the top or bottom of the file. Common malicious functions includebase64_decode,eval,gzinflate,str_rot13, orpreg_replacewith/emodifier.wp-config.php: Check for any unauthorized code..htaccess: Look for unusual rewrite rules or redirects you didn’t add.- New Files/Folders: Scan for any recently added files or directories that you don’t recognize, particularly in
wp-content/uploadsorwp-includes.
4. Check Your WordPress Database
Malware can also reside in your database. Access it via phpMyAdmin.
wp_postsandwp_optionstables: Look for spammy content, hidden links, or encoded strings in post content, comments, or site options.wp_userstable: Check for any new, unauthorized administrator accounts.
5. Use a WordPress Security Scanner
While manual checks are important, automated scanners can help identify hidden infections.
- Sucuri SiteCheck: https://sitecheck.sucuri.net/ – A free online scanner that can detect many types of malware and blacklisting.
- MalCare Scanner: Many security plugins offer robust scanning capabilities that can find hidden malware.
Step-by-Step Removal Guide
Removing the WordPress Pharma Hack requires a systematic approach. Before you begin, create a complete backup of your website (files and database). This is crucial in case something goes wrong.
Step 1: Put Your Site in Maintenance Mode
This prevents further damage and hides the compromised site from visitors while you work. You can use a plugin or manually create a maintenance.php file.
Step 2: Remove All Core WordPress Files (Except wp-config.php and wp-content)
This might sound drastic, but it ensures you remove any infected core files. Download a fresh copy of WordPress from wordpress.org.
- Delete all files and folders in your WordPress root directory except
wp-config.phpand thewp-contentfolder. - Upload the fresh WordPress core files (from the downloaded zip) to your root directory.
Step 3: Clean wp-config.php and .htaccess
wp-config.php: Open this file and carefully remove any suspicious code. It should primarily contain database connection details and WordPress settings. If unsure, compare it to a cleanwp-config-sample.phpfile from a fresh WordPress download..htaccess: Delete the existing.htaccessfile and create a new one with the default WordPress rules:# BEGIN WordPress <IfModule mod_rewrite.c> RewriteEngine On RewriteBase / RewriteRule ^index\.php$ - [L] RewriteCond %{REQUEST_FILENAME} !-f RewriteCond %{REQUEST_FILENAME} !-d RewriteRule . /index.php [L] </IfModule> # END WordPress
Step 4: Clean Your wp-content Folder (Themes, Plugins, Uploads)
This is where much of the malicious code often hides.
- Themes: If you have custom themes, download them and scan them thoroughly for malicious code. If you use a premium or free theme, delete it and reinstall a fresh copy from a trusted source. Remove any unused themes.
- Plugins: Delete all plugins and reinstall fresh copies from the WordPress plugin repository or trusted premium sources. Remove any unused plugins.
- Uploads Folder: Scan your
wp-content/uploadsfolder for any suspicious PHP files (e.g.,shell.php,cache.php, or files with random names). Uploads should typically only contain images and media. Delete any suspicious files.
Step 5: Clean Your WordPress Database
This is a critical step as the hack often injects spam directly into your database.
- Remove Spammy Users: In phpMyAdmin, go to the
wp_userstable and delete any unauthorized user accounts. - Clean
wp_postsandwp_options: Search for and remove any spammy pharmaceutical keywords, hidden links, or suspicious encoded strings in thepost_contentcolumn ofwp_postsandoption_valueofwp_options. This often requires careful manual inspection or using a security plugin that can clean the database.
Step 6: Re-upload Clean Files and Change All Passwords
- Re-upload the clean
wp-config.phpand the newly generated.htaccessfile. - Change ALL Passwords: This is paramount. Change your WordPress admin password, database password, FTP password, hosting control panel password, and any other passwords associated with your website.
Step 7: Request a Review in Google Search Console
Once you are confident your site is clean, go to Google Search Console (under Security & Manual Actions) and request a review. Google will re-crawl your site and remove the “This site may be hacked” warning if it’s clean.
Prevention Strategies for the Future
After a successful cleanup, implement these measures to prevent future infections:
- Regular Backups: Implement a robust, automated backup solution (both files and database) and store backups off-site.
- Strong Passwords and 2FA: Enforce strong passwords for all users and implement Two-Factor Authentication.
- Keep Everything Updated: Regularly update WordPress core, themes, and plugins. Remove unused themes and plugins.
- Use a Reputable Security Plugin: Install and configure a comprehensive security plugin (e.g., Wordfence, Sucuri, MalCare) for real-time scanning, firewall protection, and login security.
- Secure Hosting: Choose a hosting provider with strong security measures, including firewalls, malware scanning, and isolated environments.
- Monitor Your Site: Regularly check your site’s health, Google Search Console, and use uptime monitoring tools.
- Disable File Editing: Add
define(\'DISALLOW_FILE_EDIT\', true);to yourwp-config.phpfile.
Conclusion
The WordPress Pharma Hack can be a daunting challenge, but with the right knowledge and a systematic approach, it is entirely curable. By following this comprehensive guide for removal and implementing robust prevention strategies, you can restore your website’s integrity, recover your SEO, and protect your online presence from future attacks. Remember, if the task feels overwhelming, professional WordPress malware removal services like Injected.Website are equipped with the expertise and tools to handle complex infections and provide guaranteed fixes, ensuring your peace of mind.





